Users
Administrators manage SlashDB users by accessing the User Definitions screen from the main menu Configure > Users.
Typically APIs require some level of authentication and authorization. SlashDB comes with a robust security mechanism, which allows to create individual accounts with varying level of access. It supports authentication with a username and password or with an API key.
Let's watch how an admin creates a new user account for john.tutorial:
Authorizations
At first, the newly created account does not have any access to any data. Later the admin adds a mapping between SlashDB account john.tutorial and an actual database login.
From then on, john.tutorial's requests will run against the database using database login "john", under the permissions as configured for that user in the database server.
By mapping SlashDB users to actual database logins:
- we leverage security mechanisms which are built into databases (GRANT, GROUPS, ROLES etc.),
- each SlashDB account can have different effective privileges on database objects (e.g. only SELECT),
- we avoid maintenance of complicated logic of permissions to resources in the API.
Authenticating proxy
URLs in SlashDB are unique references to data. As a result optionally we can integrate the API service with an authorization system that would decide if incoming request should be sent to SlashDB. Solutions like that are typically implemented using authenticating proxies in conjunction with single sign-on and entitlement systems. If you require this level of integration please contact us.
User Definitions list
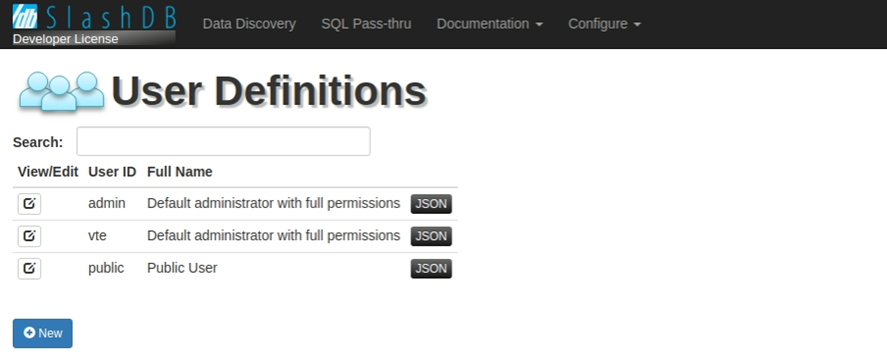
The User Definitions page provides a list all of users already setup in SlashDB.
Special accounts
admin - this is an account with administrative privileges and access to all system features. However, it does not have automatic authorization to data, which has to be configured with a database mapping.
public - acts like a regular account, but does not require any authentication. Just like a regular account it has to be configured with the mapping to access data.
View/Edit
The  button allows users to edit user details.
button allows users to edit user details.
User ID
This column lists the name of the users.
API key
If API key is not set then this method of authentication is disabled for that user. You can set your API key manually or generate random 32-character string using button Random.
Full Name
Use this column for a full name of a user or a description of a client application.
JSON
The  icon will retrieve an individual user configuration in JSON representation. The same API can be used programmatically - i.e. for integration with third party authentication systems.
icon will retrieve an individual user configuration in JSON representation. The same API can be used programmatically - i.e. for integration with third party authentication systems.
Search bar
The Search field allows users to search users already setup in SlashDB. To conduct a search, input the search terms in the field and the users list will automatically filter down to the matching results. Only fields User ID and Full Name are searched.
Adding a new user
1. To add a new user account, click the  button. The screen below will appear.
button. The screen below will appear.
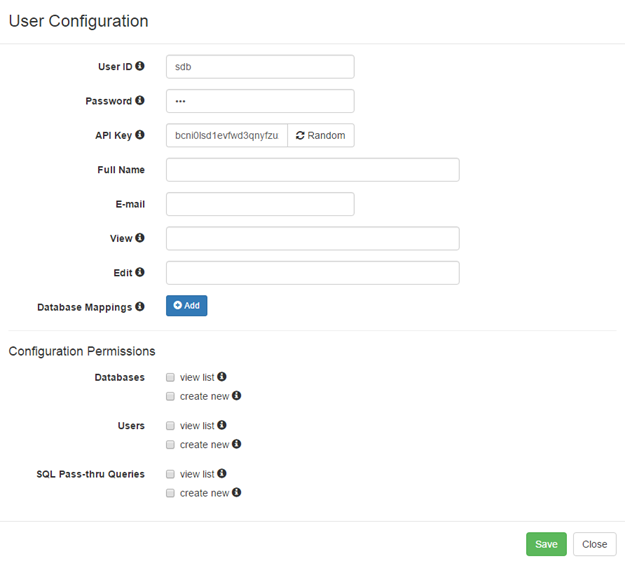
2. Fill out the User ID field to give the user a name and a password in the Password field.
3. The API Key identifies the user, so it has to be unique. The Random button generates a random sequence of characters for the API Key. The API key is a preferred way to authenticate into SlashDB programmatically.
4. Fill out the rest of the fields on the screen. Hover your mouse cursor over the  icon to learn more about the field's purpose and configuration tips.
icon to learn more about the field's purpose and configuration tips.
5. To give a user permissions to a database, click the  button to configure Database Mappings.
button to configure Database Mappings.
Select a Database ID from the drop-down list. Then enter login and password for that database. These are actual database server credentials under which this SlashDB user will be operating.
If a database doesn't require or does not support logins (such as SQLite databases), leave the db user and db password fields blank.
6. Configuration permissions determine which parts of the configuration system the user will be able view and/or create.
For regular users and applications leave those unchecked. For power users and secondary admins select the appropriate permissions.